Confidential Computing Saves the Game and Gamer’s PII
Esports has become one of the fastest-growing activities in the world, and now, thanks to cloud services and technologies, it’s only going to continue to skyrocket. Cloud technology helps boost online streaming platforms and has given esports players access to high-end games, a virtual arena in which they can compete, and a variety of other interactive features. In this article, we’ll explore how esports has been revolutionized by cloud services and technologies.
Cloud Computing Makes Esports Faster & Easier
Cloud computing allows developers to utilize large servers and scalable computing power in order to host their games or services without the need for expensive hardware or internet connections. Thanks to cloud hosting solutions, competitive gaming becomes faster and easier than ever before — especially when players are engaging in gaming competitions across multiple regions. Esports involves more than just being an individual player; gaming communities often form around big names within CS: GO (Counter Strike Global Offensive), League of Legends (LoL), Overwatch, Dota 2, and many more that require hundreds and even thousands of gamers from all over the world participating at once! With cloud services, these communities can easily expand their user base as fast as needed with highly scalable solutions.
More Engaging Gameplay through Cloud Realities
Today’s modern gamers expect more engagement from their favorite games than ever before — not just visually but also through audio cues such as sound effects or binaural noise. To increase player engagement further, publishers are now embracing augmented reality (AR) capabilities with 3D avatars making real-time decisions based on data collected within the match while using voice control functions embedded into virtual assistants like Amazon Alexa — which is all made possible through video game streaming software leveraging cloud computing power. This way teams can enjoy exciting new ways of playing together without long downtime between circuits or slow loading time when trying out weapons or battle strategies while immersed in AR environments they create themselves using Cloud technologies.
Increased Spectator Engagement & Interaction
Just like any other professional sport, there are viewers who show up just to spectate–and Cloud technologies provide extra insight into what’s happening within a game as well as enabling spectator-specific features such as exclusive avatar costumes for those watching live streams. Plus with better moderation tools broadcasters can keep the bad language out ensuring more polite conversations under their channel resulting in higher viewership numbers overall!
Confidential Computing Use Cases for eSports
Esports has grown rapidly over the last few years, and as with any other industry, security threats have become more of an issue. Swatting and Personally Identifiable Information (PII) protection are two of the most significant concerns for esports organizations today.
Preventing Swatting in Esports
Swatting is a malicious prank where someone calls emergency services to report a fake crime at a person’s address in order to trigger a heavily armed law enforcement response to the location. This type of attack has been used several times against streamers and professional players in recent years, resulting in fear and disruption for those involved.
To help prevent this from happening, organizations should take steps to protect their players from becoming targets of swatters. Companies can provide their players with encrypted communication methods like private chat rooms or secure messaging apps that allow players to keep their conversations away from prying eyes. They can also encourage better privacy practices by teaching their players how to protect information online such as using anonymous usernames and safeguarding their digital identities from hackers.
Protecting Personal Information (PII)
Esports also poses another challenge — protecting players’ Personally Identifiable Information (PII). This includes names, addresses, emails, phone numbers, and financial data that need to be kept safe from attackers who could use it for malicious purposes such as identity theft or fraud. To help prevent any unauthorized access to these sensitive pieces of information, companies should implement strong data protection measures such as using encryption technologies and implementing strict user authentication processes when collecting PII. Companies should also ensure they have updated their Privacy Policies so they remain compliant with any applicable laws or regulations related to data protection too.
Protecting PII, Game State, and Codebase & Preventing Swatting Using CC
Confidential Computing (CC) offers solutions to some of the security concerns of Esports. At SafeLiShare, we secure two essentials: code base and data with runtime security.
The use of Identity Based Encryption (IBE) or its extension WIBE (Wildcard Identity Based Encryption) would protect players from swatting attacks. In IBE, a player’s known identity information, e.g., email address, can be used to generate a public key which may then be used to encrypt the player’s communications. The corresponding private key can be generated by the game server and used to decrypt the communications. The weakness of this approach is that the server generating the private key must be a trusted entity. This trust is engendered by housing the server in a secure enclave protected by Trusted Execution Environment (TEE) or Confidential Computing (CC) technology. Similarly, communications for multiple players can be encrypted using WIBE based on their known identity information.
Another concern of Esports is protecting the game state from hacking attacks. If the game server runs in a secure enclave, the enclave using TEE or CC technology becomes a protected and isolated environment that is free of malware and impervious to external threats. Secure enclave-based executions produce audit logs that can be used to verify that the execution was free of intrusions and secure, thereby ensuring players and administrators that the game state was protected.
A final benefit of CC technology in Esports is protecting the codebase that is executing at any given time. Esports platforms and administrators often need to assure players and officials that the codebase has not been altered by any external party. CC allows a cryptographic digest of a codebase to be designated as the baseline image. A secure enclave may then be created under the policy that a given codebase could be executed in the enclave only if it matches–bit for a bit– the baseline image.
The use of CC technology in Esports offers exciting opportunities from protecting players’ personal and game data, counter swatting attacks, to protecting the game state and codebase of games.
If this topic is intriguing to you or you want to learn more about it, join us at the live stream here and Youtube premiere.
About SafeLiShare
Safelishare is fundamentally redefining today’s data and application workload infrastructure to provide complete data residency, sovereignty and compliance control transparently encrypt all customer’s data in use, in transit and at rest. If you would you like to how how we secure your code base or data base, send us an email at info@safelishare.com for a quick demo.
Suggested for you
February 21, 2024
RSAC 2024: What’s New
SafeLiShare unveils groundbreaking AI-powered solutions: the AI Sandbox and Privacy Guard in RSAC 2024
February 21, 2024
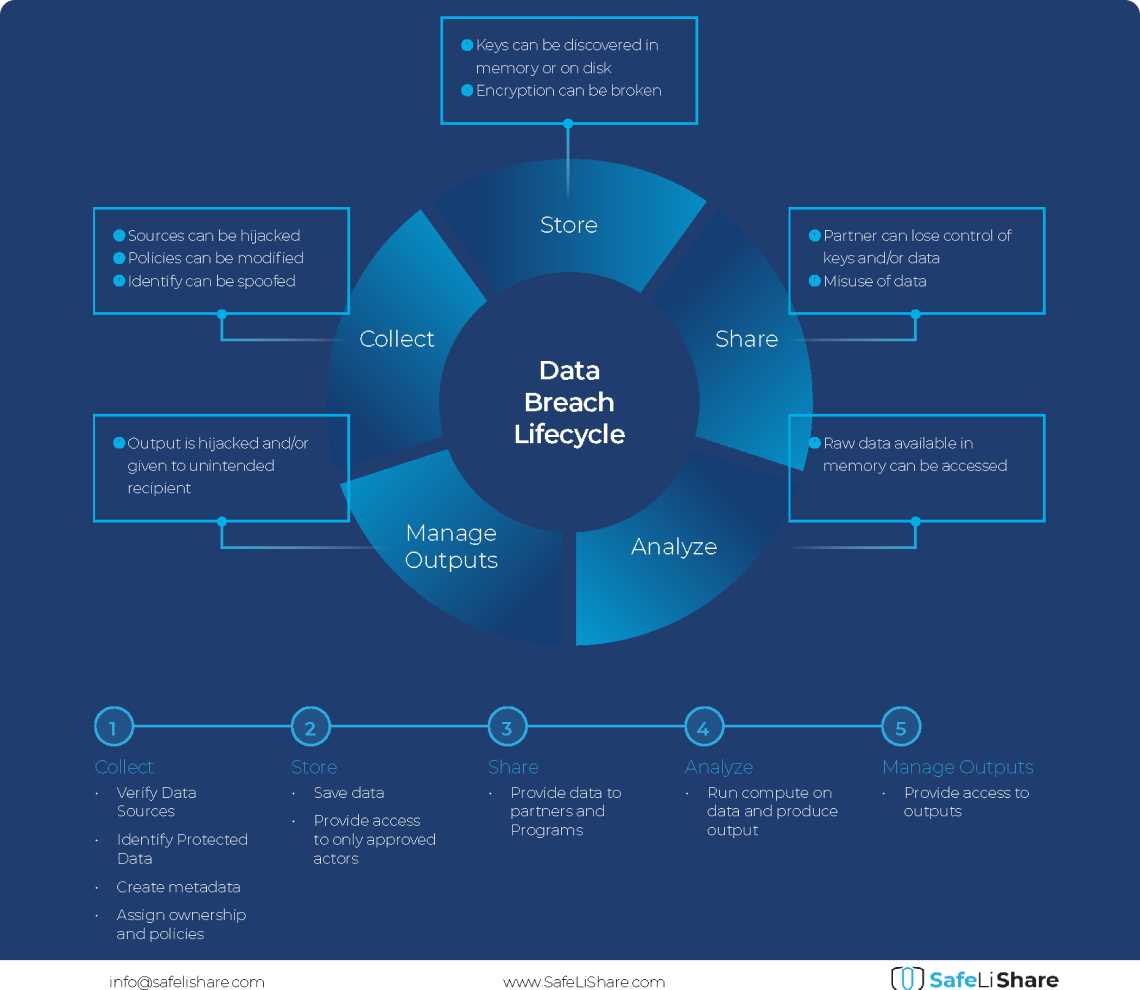
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.