Confidential Clean Rooms
SafeLiShare’s clean rooms ensure security and privacy on both the data and models used within data cleanrooms are cryptographically verified when collaborating on data while preserving privacy.
Moreover, all asset owners can use different cloud platforms without cloud IT resources and processes are immutable, auditable, and trackable.
- Computationally enforced policies govern who can do what with data, for how long
- Keep data protection for multi-party data sharing
- Automate a series of inter-connected secure enclaves with access control and key management
- Assure data usage and enforce continuous GRC
Enables unstructured data sharing with verifiability
Improved Learning Through Data Aggregation
SafeLiShare enables confidential federated learning with multiple parties to collaboratively learn a shared prediction model without exchanging their data and outputs, which improves user privacy and reduces bandwidth costs.
A Series of Interconnected Secure Enclaves
Control and manage the keys used decrypt the registered assets and control the ensuing computations. SafeLiShare delivers end to end protection for sensitive and private information brought into the clean room is ensured as assets are re-encrypted when exiting the clean room.
Secure AI/ML Models and Federated Workflows
Allows users to securely manage access to their data across multiple systems, applications, and services in data collaboration. SafeLiShare makes it easy to adhere to different data policies and permissions from a single pane of control.
Complete Visibility and Full Control
SafeLiShare’s management plane integrates data inputs to produce downstream decision-making process or additional insights.
Featured Collateral
Confidential Clean Room: Use Cases
The confidential clean room is designed to maintain confidentiality and privacy by restricting physical and virtual access, while cloud computing provides scalable and flexible resources for data processing and analysis. How do you protect data from cyber attacks and data exfiltrations using privacy preserving technology with immutable and continuous compliance.

“With TEE nearly ubiquitous, the upcoming implementation with the Azure Confidential Container instances remediate the industries’ challenge to reverse the never-ending cycles of adding more protections from outside in.”
Graham Bury, Principal PM Manager
Micrsoft Azure Confidential Computing
People also ask
Why is SafeLiShare’s encrypted data clean room different from other data clean room approach?
What do I need to show proof for GDPR legal compliance?
How does SafeLiShare provide audit trail and access report for GDPR and HIPAA compliance?
Additional materials
February 21, 2024
RSAC 2024: What’s New
SafeLiShare unveils groundbreaking AI-powered solutions: the AI Sandbox and Privacy Guard in RSAC 2024
February 21, 2024
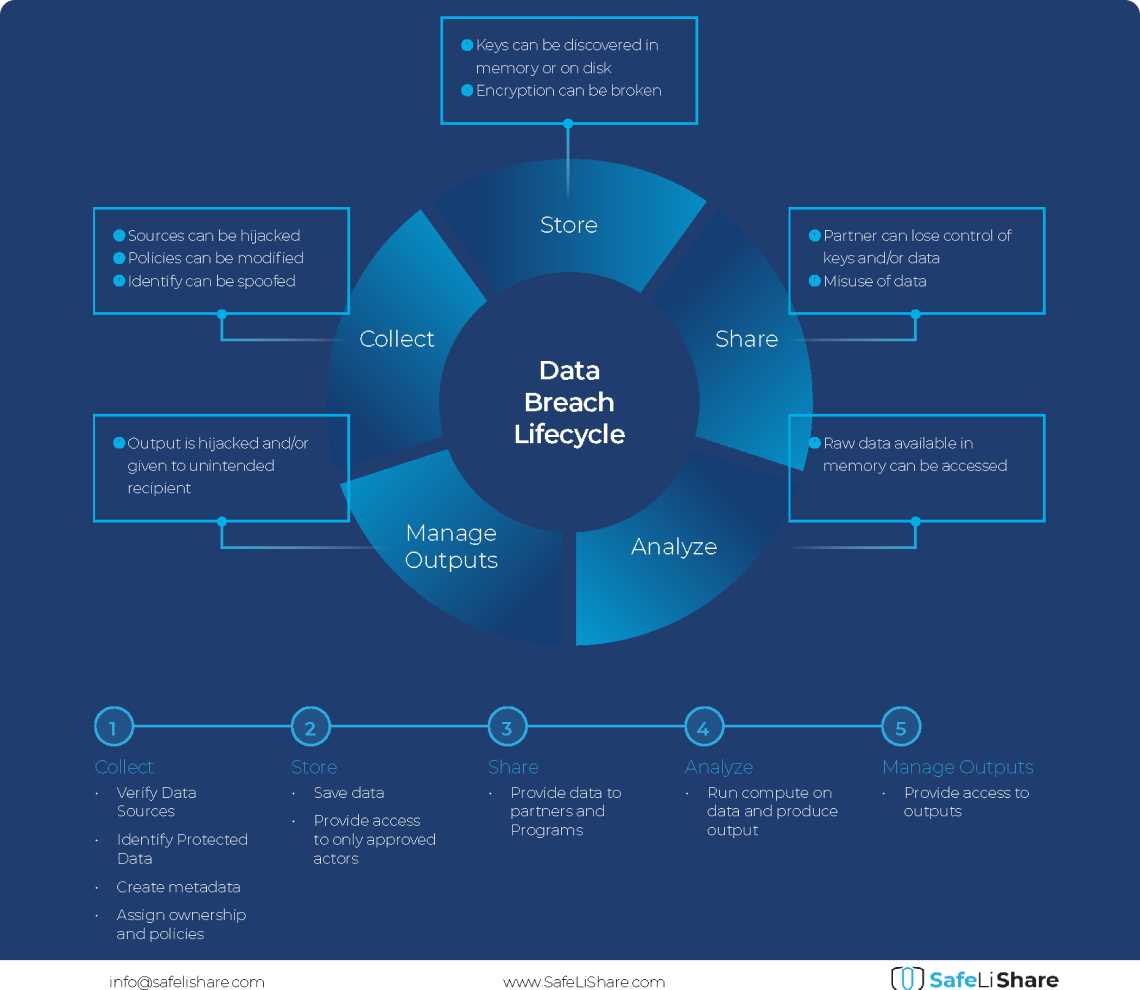
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.
Experience secure collaborative data sharing today.
Maximize accessibility and monetization of sensitive, regulated, or confidential data without compromise.