Powerful Data-Sharing and Privacy-Preservation in Healthcare
SafeLiShare enables secure, authorized transmission and collaboration on protected health information (PHI) between healthcare providers, medical researchers and other authorized parties with compliance ready audit logs.
- Understand the value and benefits of using shared data;
- Achieve HIPAA compliance with end-to-end encryption;
- Get better quality insights from shared data and remain HIPAA compliant;
- Privacy by design with PHI hardened isolated environments.
Monetize data value, drive efficiency, and reduce risk across your B2B network
Multi-Party Healthcare Data Sharing
SafeLiShare Confidential Computing allows healthcare stakeholders to securely access, store, and share patient data. This helps improve the speed of the clinical trial process; help healthcare organizations make better decisions through enhanced analytics and research.
Run Applications and Data within Secure Enclaves
SafeLiShare uses cloud vault storage to store the client keys. During the sharing phase, the keys are protected using keys protected by secure enclaves. Data and application are both encrypted with programmable key management.
Policy Enforcement & Auditing Beyond VDI farm
SafeLiShare policy enforcement and access logger extend compliance controls with privacy rules like GDPR and HIPAA.
Always-on Protection on Applications and Data
With SafeLiShare you have full visibility and control on users. Using cryptographic keys, designate programs accessing certain sets of data without exception.

“SafeLiShare is a technical implementation toward compliance. The realization of value was almost immediate - encryption from start to finish without de-identification going on in the secure enclave that saves the lengthy and labor intensive data prepping and masking prior to sharing.”
Vasanth Thangaraju, Vice President, Product & Technology
RxLive
Displace Costly Workflow with De-Identification
- Legacy safe harbor data mapping and randomization of PII is inefficient
- 10-15% of IT budget spending on de-ID
- Compliance mandate built-in privacy, governance, and access control for covered entities and data relay agencies
Expedited Partner Ecosystems of Care
- Data management becomes an even bigger asset
- Variability, accuracy, and control across the entire partner ecosystems
- Real time data access for data science and advanced analytics at cloud scale
- Evidence-based restrictions for compliant collaboration
Remote attestation of data accuracy, lineage and compliance
- Tamper-proof data access audit on share data and apps with all parties
- HIPAA, PHI and PII access compliance
- Improve healthcare outcome and the patient experience
People also ask
How is data shared in Healthcare? Can SafeLiShare provide ONC-ATCB required audit logs?
What is the de-identification alternative?
How is de-identification used in Healthcare?
Additional materials
February 21, 2024
RSAC 2024: What’s New
SafeLiShare unveils groundbreaking AI-powered solutions: the AI Sandbox and Privacy Guard in RSAC 2024
February 21, 2024
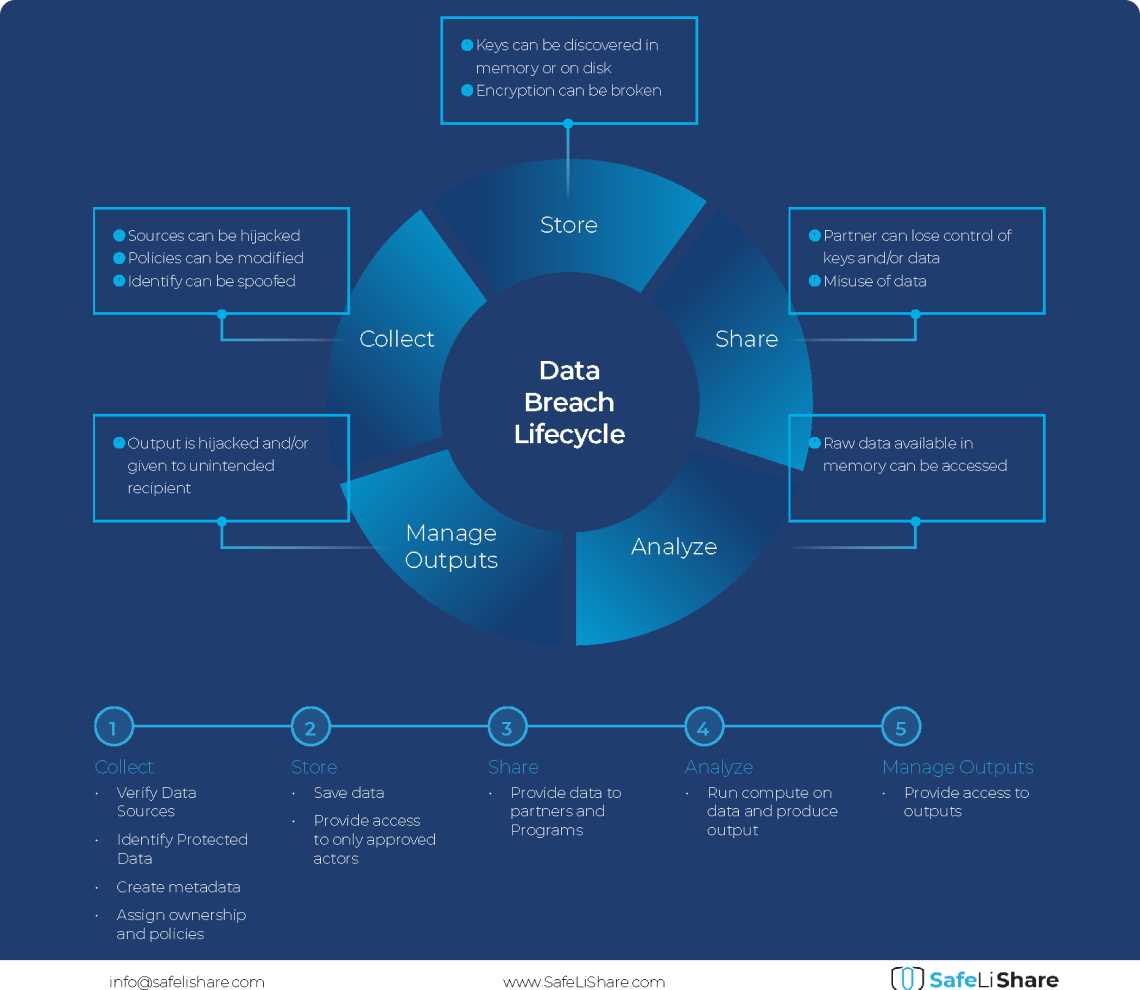
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.
Experience secure collaborative data sharing today.
Maximize accessibility and monetization of sensitive, regulated, or confidential data without compromise.