Defining Confidential Computing
Confidential Computing (CC) refers to a set of technologies and practices that aim to protect data while it is being processed in computer systems. It involves encrypting data while it is in use, as well as isolating it from other processes and applications on the same system.
There are many powerful and interesting ideas engendered by this model of computing. For example, the model allows applications to process sensitive data in a protected environment without exposing it to other processes and applications on the same system.
An important notion in CC is the hardware root of trust, achieved by embedding a set of private keys into the hardware. These keys can be used to establish and verify the authenticity and the integrity of the hardware. Isolated and protected environments created using Confidential Computing can be used to generate keys that encrypt data which can only be decrypted inside an isolated and protected environment. In this sense, the custody of the data is effectively given to the system.
This can have far reaching consequences for compliance and audit. A key feature of computing environments created using CC is that immutable and verifiable audit logs can be generated of the actors and activities inside such environments. Establishing a chain of data custody from enterprises to hardware created environments raises several new issues and concerns including notions of program identity and authorizing access privileges to computer programs.
Suggested for you
February 21, 2024
RSAC 2024: What’s New
SafeLiShare unveils groundbreaking AI-powered solutions: the AI Sandbox and Privacy Guard in RSAC 2024
February 21, 2024
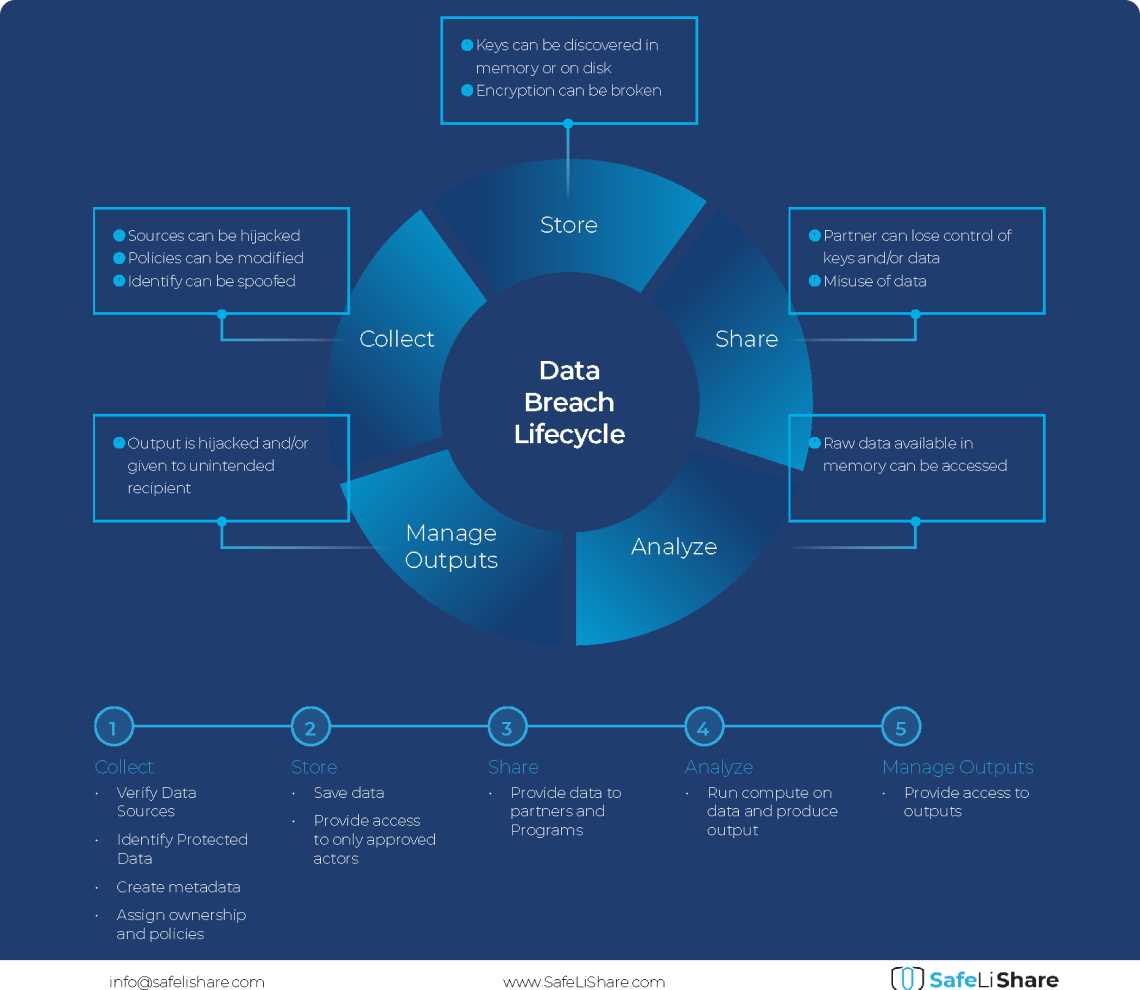
Cloud Data Breach Lifecycle Explained
During the data life cycle, sensitive information may be exposed to vulnerabilities in transfer, storage, and processing activities.

February 21, 2024
Bring Compute to Data
Predicting cloud data egress costs can be a daunting task, often leading to unexpected expenses post-collaboration and inference.
February 21, 2024
Zero Trust and LLM: Better Together
Cloud analytics inference and Zero Trust security principles are synergistic components that significantly enhance data-driven decision-making and cybersecurity resilience.